Barracuda FREE Email Threat Scanner
Detect email threats that already exist within your email environment
Overview:
Over 95% of Office 365 mailboxes harbor malicious emails.
Many of these email threats stealthily slip past the email gateway. Threats like ransomware, spear phishing, and account takeover put your organization and employees at significant risk. In fact, undetected email threats cost businesses over $300 million per month.
Find out what's hiding in your inbox.
It's critical to assess and understand your email security vulnerabilities. Using artificial intelligence and API integration with Office 365, the Barracuda Email Threat Scanner quickly and effectively finds social engineering attacks currently sitting in your mailboxes.
How Barracuda Networks Can Help
Barracuda Email Threat Scanner is a free online service that scans all your Office 365 emails and identifies these dormant threats without any impact on your system's performance. Use it to:
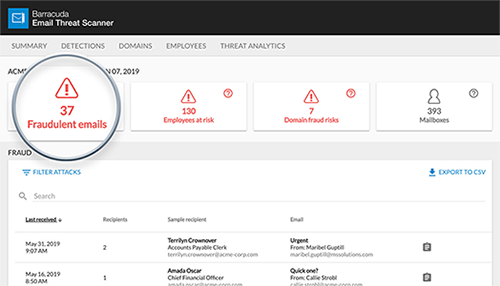
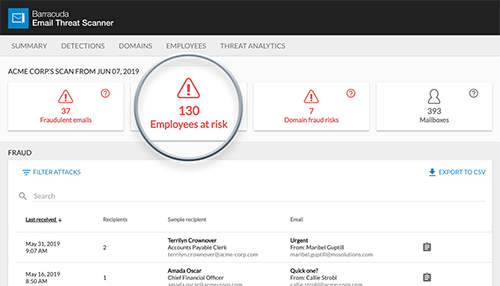
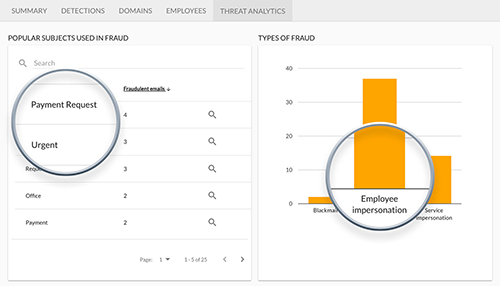
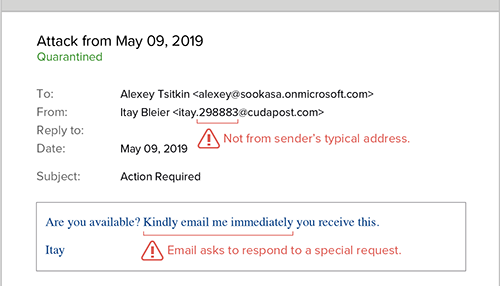
- Find spear phishing, account takeover, business email compromise, impersonation, and other cyber fraud attacks that impersonate trusted senders and are designed to trick employees into clicking on a malicious link, sharing confidential information, or even wiring money to the attacker
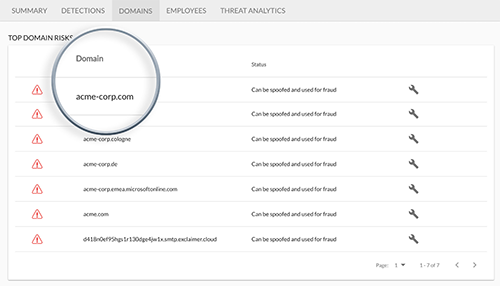
- Prevent domain fraud by identifying domains that are at risk of spoofing and other fraud
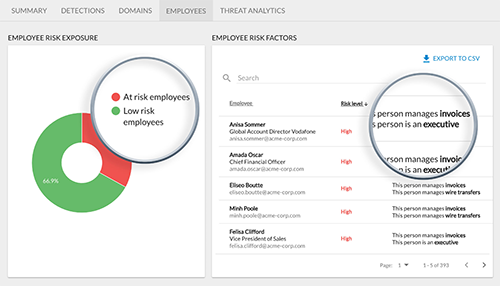
- Identify high-risk employees who are most likely to be targeted by spear phishing and business email compromise attacks
- Detect email threats that already exist with within your email environment
Run a FREE Email Threat Scan
Run your FREE Email Threat Scan today. Discover how exposed you are to new threats, and reveal the fraudulent emails already in your mail system.
Sign Up for a Free Email Threat Scan
How many threats are already in your corporate mail system? Sign up below for a FREE Email Threat Scan that will check not only your exposure to new threats but also scan all of the emails already in your mail system.