Barracuda Networks SSL VPN 880
Remote, Authenticated Access to Applications and Data

Sorry, this product is no longer available, replaced by the CloudGen Firewall F-Series Appliances.
 Barracuda SSL VPN Overview:
Barracuda SSL VPN Overview:
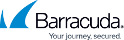
The Barracuda SSL VPN is an integrated hardware and software solution enabling secure, clientless remote access to internal network resources from any Web browser. Designed for remote employees and road warriors, the Barracuda SSL VPN provides comprehensive control over file systems and Web-based applications requiring external access. The Barracuda SSL VPN integrates with third-party authentication mechanisms to control user access levels and provides single sign-on.
- Enables access to corporate intranets, file systems or other Web-based applications
- Tracks resource access through auditing and reporting facilities
- Scans uploaded files for viruses and malware
- Leverages multi-factor, layered authentication mechanisms, including RSA SecurID tokens
- Integrates with existing Active Directory and LDAP directories
- Utilizes policies for granular access control framework
- Supports any Web browser on PC or Mac
The Barracuda Advantage
- No per-user fees
- Easy to use
- Easy to deploy
- Added security with built-in virus scanning
- Anytime, anywhere access
Product Spotlight
- Simple remote-worker access to corporate applications and data
- Fast and secure access from virtual any mobile device
- Remote access to MS Exchange, MS SharePoint and Windows File Shares
- Simple mobile device configuration, ideal for BYODs
- Powerful two-factor and 'progressive' authentication options
Easy as Opening a Web BrowserThe Barracuda SSL VPN makes it easy for remote users to access internal applications and files. Unlike traditional VPN technologies, the Barracuda SSL VPN does not require any additional client software or complicated settings. Logging in from home or the road requires only a web browser and Internet connection. Upon login, users are presented with a portal of internal web applications or file shares. More advanced applications like Remote Desktop Services or Citrix XenApp are available to users running Java. |
|
Comprehensive AuthenticationAdministrators have complete control over user access with the option of further securing resources with secondary authentication. Possibilities include sending one-time passcodes to mobile phones (including Google Authenticator), prompting with security questions, or integrating with advanced authentication systems like hardware tokens, RADIUS, and other additional security methods. Risk Based Authentication allows the use of extra authentication for high risk applications. |
|
Comfort in a secure networkThe Barracuda SSL VPN provides extra security layers, including the ability to reverse-proxy Exchange ActiveSync traffic to keep Windows servers safely inside the network perimeter. Integrated antivirus protection secures file uploads to keep malware out of the network. Built on a hardened platform, the Barracuda SSL VPN is the ideal replacement for traditional software-based remote access gateways. |
Powerful, Complete Solution
Installed in a matter of minutes, the Barracuda SSL VPN enables complete control over the resources designated for external access, such as internal Web applications, file systems and other applications. From any Web browser, users connect to internal Web sites through a built-in reverse proxy for access to network file shares. Richer support for SSL tunneling is enabled through the Barracuda SSL VPN Agent, a lightweight Java client that supports common remote applications, including Remote Desktop, VNC, NX, SSH and Telnet.
For complete network layer access, the Barracuda SSL VPN includes the Barracuda Network Connector, an installable VPN client for TCP or UDP connectivity. With the Barracuda Network Connector, users gain SSL access to legacy client/server application during a VPN session.
With robust security and auditing features, administrators define custom policies to govern resource access to particular users or groups while tracking user activity. For added security, files uploaded during a VPN session to network file shares or internal Web sites are scanned for viruses and other malware to prevent infections of critical network resources.
Best-of-Breed Access Control
Remote access by nature can be risky exposing network resources across the Internet. However the Barracuda SSL VPN mitigates these risks by tightly controlling user access through a full suite of authentication mechanisms and support for third-party authentication, such as Active Directory or LDAP. Administrators have the option to layering security by enforcing the use of PIN numbers, hardware tokens, client certificates and other forms of secure authentication on top of AD or LDAP.
By restricting usage to internal resources upon presenting the correct credentials and token code, an organization securely manages external access to network resources. The policy-based access control framework integrates into existing AD or LDAP schema to grant users rights and permissions. For added granularity, administrators have the option of setting policy to set and limit network resources by AD or LDAP rights. Once access is granted, the administrator monitors resource access from VPN clients by the use of the auditing feature.
Easy-to-use, secure network access for business travelers, remote workers, and mobile users
Your army of road warriors and remote workers require a quick, flexible, reliable and completely secure way to connect to your internal enterprise applications, information and network resources. They want to do this from anywhere in the world, at any time and from any suitable device. The Barracuda SSL VPN provides the security and connectivity to deliver this access, via a web browser or virtually any mobile device.
Benefits:
|
|
|
Easy and Secure Mobile Access
Today, corporate data and applications need to be available anytime, from anywhere. As BYODs become commonplace, providing easy access for mobile devices not subject to network policy enforcement -- while ensuring corporate data is secure -- is critical. The Barracuda SSL VPN delivers fast and secure access while ensuring that a seamless and simple end-user experience reduces support overhead.
Key Features: Mobile Device Support

Features:
Mobile Device Support
The Barracuda SSL VPN allows remote workers to securely access an organization's applications and files from virtually any mobile device, via an easy-to-use mobile portal. Security is ensured through powerful multi-factor authentication options, while ease-of-use ensures low support costs. In addition, the device configuration feature allows easy configuration of iPhones, iPads and Mac devices for exchange, mail, LDAP, Webclips, Client Certificates, IPsec, and PPTP. Windows devices can also be configured.
Granular Resource Management
The Barracuda SSL VPN integrates a powerful engine that enables administrators to selectively authorize traffic to approved resources. The device integrates with Active Directory, LDAP, and other user databases, permitting administrators to define granular policies that allow specific users and groups to access network resources. Administrators can configure access to resources such as intranet sites, mapped network drives, applications like RDP, SSH/SFTP, CITRIX XenApp, and others.
Multi-Factor Authentication
Remote users are required to properly identify themselves before obtaining entry to the network to prevent unauthorised access. The Barracuda SSL VPN can be configured to enforce a combination of authentication schemes including Active Directory passwords, hardware tokens, client certificates, and PIN numbers. Moreover, the Barracuda SSL VPN supports RSA SecurID, VASCO, Safeword, and CryptoCard authentication servers through RADIUS integration for access using a one-time password token. This security ensures that accessing the Barracuda SSL VPN from any web browser is backed by the protection of a strong authentication policy that allows only authorised users to enter the network.
Network Access Control
Remote users can access network resources from a variety of end-points or client machines including shared computers. The Barracuda SSL VPN provides extensive network access control methods that will ensure a computer requesting remote access adheres to established security policies based on the operating system, web browser version, and other connection parameters before permitting network access.
Barracuda Network Connector
Designed for applications using UDP, the Barracuda Network Connector is a secure IP tunneling client installed on users' workstations or laptops. The Barracuda Network Connector creates an IP connection to the Barracuda SSL VPN appliance and has a fully routed VPN connection to the remote network. This streams content from the remote network and allows the use of any TCP or UDP application such as legacy client/server applications. The Barracuda Network connector also supports password, PIN, and RADIUS authentication for added security.
Hardware Token Authentication
The Barracuda SSL VPN supports RSA SecurID, VASCO, Safeword, and CryptoCard authentication servers through RADIUS integration. Hardware token authentication supports access using one time password (OTP) tokens.
Single Sign-On
The Barracuda SSL VPN integrates with user databases via LDAP, RADIUS, Active Directory, and NIS. Using central user accounts supports Single Sign-On while avoiding having to duplicate user data. The Barracuda SSL VPN can pass users' Active Directory credentials to the remote desktop session for true Single Sign-On. For transparent authentication when using reverse-proxy web forwarding, intranet websites can be launched that pass users' credentials to web applications.
Reporting and Auditing
System administrators can easily view logs and generate reports for clear visibility into remote access. The Barracuda SSL VPN generates reports on VPN use, users, resource activity, and more with no database administration or other equipment required. All resource access through the Barracuda SSL VPN is audited. Real-time reports display privilege use, failed logons, file, and intranet use, as well as other information. The status page also provides statistics about resource use.
Clientless Remote Access
Unlike traditional IPsec-based VPNs that require client software installed on remote machines, the Barracuda SSL VPN provides secure remote access to network resources from any web browser. This removes the overhead of installing and maintaining clients and permits secure access from any operating system that can support a standard web browser. SSL technology also eliminates some of the deployment issues around IPsec VPN technology like IP address conflicts, NAT traversal, and DNS issues. Some features require the use of Java plugin for clientless access.
Web Portal
A web portal provides remote users with easy access to their assigned resources. Navigation is so easy that users in the office often prefer use the portal to access their network resources as well.
Multiple User Realms
Administrators use realms when an organization has multiple user databases. Realms let the Barracuda SSL VPN authenticate against multiple domain servers and directories such as LDAP and NIS.
SSL Tunnelling
The Barracuda SSL VPN securely connects remote users through SSL-encrypted tunnels from any web browser. No client software is necessary. However, for richer tunnelling, the Barracuda SSL VPN offers the Barracuda SSL VPN agent, a lightweight Java tunnelling client. This agent supports remote applications such as Remote Desktop Services, Citrix XenApp, VNC, NX, SSH, and Telnet.
Antivirus
The Barracuda SSL VPN automatically scans files uploaded to the network file system and from intranet web applications for viruses, spyware, and other malware. Barracuda Energize Updates keep virus definitions current in real time to prevent even the latest malware from uploading to the network.
Virtual Keyboard
The virtual on-screen keyboard is a security feature that defends against key-logging attacks. The virtual keyboard echoes characters the user clicks on.
Automatic Cache Cleaning
A cache-cleaning utility automatically clears session data from the user's web cache and history when the user logs out or disconnects. Cache cleaning prevents unauthorised exposure of information when users access the Barracuda SSL VPN from public or shared computers.
Access Resources in Other Networks
The Barracuda SSL VPN Server Agent streamlines connections to services at remote sites without the risks and burden of using a fully routed IPsec connection. The Barracuda SSL VPN Server Agent directly connects to services hosted on remote networks from the Barracuda SSL VPN.
Google Authenticator
Google Authenticator offers an easy way to use time-based, single-use passwords (TOPT) using Google infrastructure and mobile apps. The authentication module can be used by itself or in combination with other authentication modules for multi-factor authentication. A new verification code is automatically generated every 30 seconds. The official Google Authenticator app is available for Android, iOS and Blackberry (version 6 or lower) devices. Third-party apps are available for almost all other mobile operating systems. This feature works on both the desktop and mobile portals.
Risk Based Authentication (RBA)
Some network environments might require additional security levels to authenticate users when they access specific high-risk SSL VPN resources. Barracuda SSL VPN provides risk-based authentication for Web Forwards, applications and SSL tunnels. Each launch of these resource types can be protected by PIN, password, or Google Authenticator. This feature works on both the desktop and mobile portals.
Model Comparison:
Available in five models, the Barracuda SSL VPN secures remote access to internal network resources from any Web browser. The Barracuda SSL VPN 180 handles up to 15 users and scales up to 1000 users with the Barracuda SSL VPN 880. These specifications are not limits of the system, but are the recommended capacity.
| Model Comparison | 180 | 280 | 380 | 480 | 680 | 880 |
|---|---|---|---|---|---|---|
| Capacity | ||||||
| Maximum Concurrent Users | 15 | 25 | 50 | 100 | 500 | 1000 |
| Hardware | ||||||
| Rackmount Chassis | 1U Mini | 1U Mini | 1U Mini | 1U Mini | 1U Fullsize | 2U Fullsize |
| Dimensions (in.) | 16.8 x 1.7 x 9 | 16.8 x 1.7 x 9 | 16.8 x 1.7 x 14 | 16.8 x 1.7 x 14 | 16.8 x 1.7 x 22.6 | 17.4 x 3.5 x 25.5 |
| Weight (lbs. / kg.) | 8 / 3.6 | 8 / 3.6 | 12 / 5.4 | 12 / 5.4 | 26 / 11.8 | 46 / 20.9 |
| Ethernet | 1x 10/100 | 1x 1GbE | 1x 1GbE | 1x 1GbE | 2x 1GbE | 2x 1GbE |
| AC Input Current (Amps) | 1.0 | 1.0 | 1.2 | 1.4 | 1.8 | 4.1 |
| Redundant Disk Array (RAID) | ||||||
| ECC Memory | ||||||
| Redundant Power Supply | Hot Swap | |||||
| Features | ||||||
| Barracuda Network Connector | ||||||
| Web Forwarding | ||||||
| Network File Access | ||||||
| Windows Explorer Mapped Drives | ||||||
| Citrix XenApp/VNC/NX/Telnet/SSH/RDP Applications | ||||||
| Single Sign-On | ||||||
| Antivirus | ||||||
| Client Access Controls | ||||||
| Active Directory/LDAP Integration | ||||||
| Layered Authentication Schemes | ||||||
| Mobile Portal | ||||||
| L2TP/IPsec, PPTP Mobile Device Support | ||||||
| Device Provisioning (Windows, Mac OS X, iOS) | ||||||
| Risk Based Authentication | ||||||
| Google Authenticator Support | ||||||
| Remote Assistance | ||||||
| Multiple User Realms | ||||||
| Barracuda SSL VPN Server Agent1 | ||||||
| Hardware Token Support | ||||||
| RADIUS Authentication | ||||||
| Syslog Logging | ||||||
| SNMP/API | ||||||
| Clustering/High Availability | ||||||
1 Not available via mobile access.
Technical Specs
![]()
Security Features
- Supports Active Directury, LDAP, NIS, and built-in user databases
- Policy-based rights management
- Multi-layered authentication schemes
- One-time password authentication via email or SMS
- Google Authenticator Support
- Risk Based Authentication
- Supports SecurID, VASCO, Safeword, and CryptoCard authentication tokens
- Supports Aladdin eToken, SafeNet iKey, and other PKI USB devices
- Client assess controls based on operating system and web browser version
- Automatic cache cleaning and logout
- Web application URL masking
- Virtual keyboard
![]()
Virus Scanning
- Virus, spyware, and malware scanning
- Decompression of archives
- File type blocking
![]()
VPN Features
- Intranet web site forwarding
- Network file system browsing
- Single Sign-On
- SSL VPN agent for clientless deployment1
- Network Connector: VPN client for IP connectivity
- Local Windows Explorer drive mapping
- Configurable SSL tunnels
- Multiple user logon realms
![]()
Mobile Support
- Customizable Mobile Portal
- Supports all common mobile devices (i.e., iOS, Android, Blackberry, Windows Phone, and Microsoft Surface)
- Provides access to corporate applications and file shares
- L2TP/IPsec and PPTP Mobile Device Configuration for Shortcuts, VPN Connections, and Active Synch / MS Exchange (iOS)
![]()
Auditing and Reporting Capabilities
- Track file, web, and network access
- Reports in PDF, CSV, and text formats
- Granular controls for access and policy
- Health monitoring
- Network utilization and appliance load statistics
Support Options
![]()
Barracuda Energize Updates
- Standard technical support
- Firmware and capability updates as required
- Automatic application definitions updates
![]()
Instant Replacement Service
- Replacement unit shipped next business day
- 24x7 technical support
- Hardware refresh every four years
Hardware Features
![]()
Connectors
- Standard VGA
- PS/2 keyboard/mouse
- Ethernet (see chart)
- Serial port (DB-9)
Views:
Front Panel
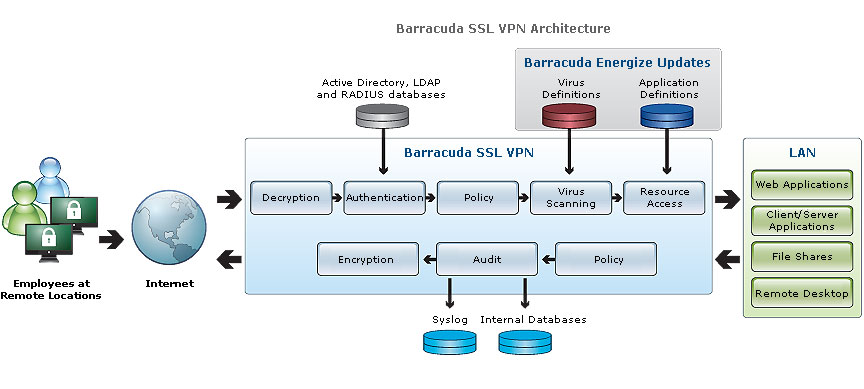
The following figure illustrates the Barracuda SSL VPN power and disk activity indicator lights for models 880:
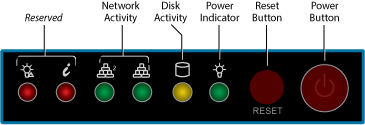
Rear Panel Ports and Connectors
The following figure illustrates the Barracuda SSL VPN rear panel ports and connectors for models 880:
Deployment:
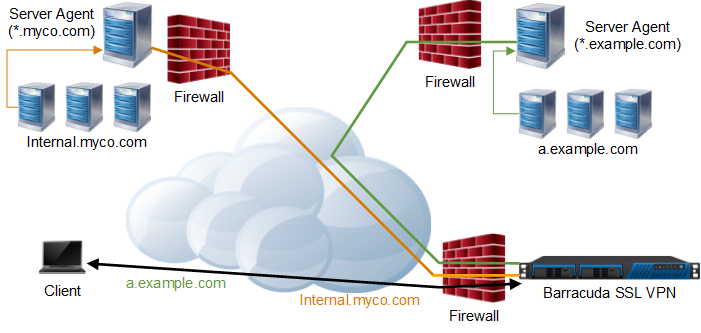
The Barracuda SSL VPN is typically deployed in the following configurations:
- Direct Access Deployment - Behind the firewall, with direct access to all intranet resources.
- Multilayer Firewall DMZ Deployment - In a DMZ between the external and internal firewall. Additional ports have to be opened on the internal firewall to access internal resources.
- Isolated Deployment - The Barracuda SSL VPN is reachable from the Internet. All resources connect via Server Agents which initiate the connection from inside the networks. No ports have to be opened.
Direct Access Deployment
The Barracuda SSL VPN is deployed behind the firewall. Only one port (443) has to be opened up by the firewall and forwarded to the SSL VPN. You have direct access to all services (authentication, file, web, etc.) in the intranet without further configuration.

Multilayer Firewall DMZ Deployment
The Barracuda SSL VPN is deployed in a DMZ behind the corporate firewall but before the internal network firewall. All access to services on the internal network requires ports to be opened on the internal firewall. By deploying the Barracuda SSL VPN between the two firewalls, another security layer is added. It is also possible to install the Server Agent on a computer in the internal network, which initiates an SSL tunnel on port 443 from the inside of the network so you can limit the ports that you must open on the internal firewall.

Isolated Deployment
The Barracuda SSL VPN is deployed and isolated from the rest of the network. All resources are located in networks which are not directly accessible by the Barracuda SSL VPN. Server Agents inside the networks initiate tunnels to the SSL VPN and act as proxies for the local resources. This deployment minimizes security implications caused by opening various ports on the firewalls to access the resources located behind them.
VPN Technologies:
Secured remote access to corporate resources through the use of a Virtual Private Network (VPN) has become an essential requirement in today's enterprise as businesses extend network access to home workers, road warriors, and business partners across the globe. One of the most efficient and cost-effective methods for fulfilling remote access requirements at many organizations is a Secure VPN, which to ensure security sends encrypted traffic over a public network such as the Internet. The two dominant types of Secure VPN technology are IPsec and SSL.
IPsec VPNs
IPsec, short for Internet Protocol Security, can run in either transport or tunnel mode, each having significantly different implications particularly with regard to security. Tunnel mode will encrypt both the header information as well as the data transmitted, whereas transport mode will encrypt only the data. Keys must be shared by both the sender and recipient in order to correctly decrypt the transmission.
IPsec works at Layer 3, or the Network Layer of the OSI Model, which enables it to operate independently of any application. An IPsec VPN creates a tunnel between two endpoints through which any number of connections and protocol types (web, email, file transfer, VoIP) can travel. The original IP data packet is re-encapsulated, so all application protocol information is hidden during the actual transmission of the data.
A typical deployment will consist of one or more VPN gateways to the secured networks. Special VPN client software must be installed on each remote access user's computer, and each VPN client must be configured to define which packets should be encrypted and which gateway is to be used for the VPN tunnel. Once connected, the client becomes a full member of the secured network, able to see and access everything just as if that system was actually physically connected to the network.
SSL VPNs
SSL (Secure Socket Layer) VPNs are often referred to as transparent, or clientless, due to the lack of any additional client-side VPN software that must be explicitly installed. The SSL components required to create a secure channel from the remote system are a part of all major web browsers, at least one of which is always already available on virtually every modern computer. The only new item that is necessary is a designated SSL VPN server, to act as the gateway between the secured network and all remote systems.
The SSL protocol operates in Layer 7, the application layer, allowing it to act as a proxy for the secured resources. Authentication of both the client and the server is achieved during the initial handshake routine where both parties identify themselves via digital certificates. The handshake process also generates session keys which are used to encrypt all traffic sent and received during a remote access session.
An SSL VPN can maintain and enforce finer-grained access control policies to individual internal resources, as well as by individual users, by intercepting all traffic between the authenticated remote system and the requested resource inside the secured network. This introduces greater flexibility since now virtually any computer with an Internet connection can be used for secure remote access - home computers, computers on customers' premises, and even Internet cafés.
IPsec vs SSL VPNs
IPsec and SSL each have their own advantages. So, what is "better" may often come down to what is most suited for your network, but many organizations are increasingly turning to SSL VPNs for the additional benefits available.
Reliance on Network Membership
Because an IPsec VPN connects on a network level, the remote computer is assigned an internal IP address upon connection and becomes a part of your intranet. For some remote users, however, the IP address space used by the IPsec VPN and/or the DNS servers for the secured network may conflict with the existing IP address space and DNS servers already in use at the remote location, or the special ports required for VPN access may be blocked.
Special NAT rules may be needed to ensure that remote sites are able to access certain internal-only systems, or special provisions made so that the internal DNS servers are accessible to the remote site without limiting existing access. When these types of issues arise, a non-trivial effort on the parts of both the remote user and the IT department may be required to resolve these issues.
No network addressing conflicts exist when an SSL VPN is used because the remote system need not maintain an address on the internal network, so no additional customizations either remotely or locally would be required.
Limiting Range of Access
Once connected via an IPsec VPN, everything that the authenticating user has access to when on-site will also be available with remote access. Any and all types of transmissions between the authenticated remote computer and the secured network are allowed, providing the remote computer with access to everything in the network with no extra permission settings required, and allowing it to be seen and accessed in return.
This does mean, however, that there is no easy way to prevent access by an offsite user to resources that should only be available to those who are physically on the premises, such as systems containing confidential data or even the printer in the CEO's office. It also introduces a possibly unsecured entry point into your network, since an infected remote computer can be the source of infiltration by a virus or other malware. As a result, most organizations prefer to limit the use of IPsec remote access whenever possible, and to only a relatively small portion of their user base.
In contrast to the wide-open access provided by an IPsec VPN, an SSL VPN operates as a proxy so that only authorised traffic destined for approved resources is allowed through, cutting off any chances of accidental infection spreading to other internal resources on the network.
Authorization can be given not just for the remote system to access the secured network, but also for only designated users to access a particular internal resource. This prevents the need to have the same access permissions forced upon all remote users, since the system administrator can now easily adjust access to specific internal resources on a user-by-user basis without performing any additional configuration changes on the networked resource.
Support and Maintenance
When using an SSL VPN, the lack of specialized VPN software clients for the end-user means that there is one less application that your IT department will have to support and maintain. SSL components are updated as part of browser maintenance, with any additional modules that may be required being dynamically downloaded during an encrypted session.
The Barracuda SSL VPN
The Barracuda SSL VPN is an integrated hardware and software solution that provides the advantages of both IPsec and SSL, enabling secure, clientless remote access to internal network resources from any web browser.
Taking only minutes to install, the Barracuda SSL VPN is extremely fast and easy to deploy to all or just some of your user base, no matter what the size of your organization. Integration with popular authentication protocols such as LDAP allows you to import user information directly from your user database or LDAP server, or you can create local accounts if you so desire. And with no client to distribute and no additional network configurations required, all you need to do now is to configure your access policies and you're ready to go.
The Barracuda SSL VPN can also provide full network connectivity using the Barracuda Network Connector, so that specific authorised users can be provided wide-open access to the entire network in a manner similar to what is provided by IPsec.
To set more secure access rules, the easy-to-use administrator interface allows you to instantly identify categories of resources such as "Web Forwards" or "Applications", and view and set policies by an individual resource (internal web applications or network shares, telnet, SSH-based access, or even remote desktop access such as RDP or VNC). Policies can also be viewed and modified for individual users (locally created or imported from LDAP) or by groups, so that when remote users log in, they will be able to tell at a glance from their own personalized home page on the Barracuda SSL VPN exactly which internal resources are available for that session.
Organizations must balance their growing remote access needs against their available IT resources, and a remote access solution must be easy to set up and maintain while having minimal impact on the IT helpdesk. By incorporating the Barracuda SSL VPN into your remote access strategy, you gain the benefits of secure remote access without the cost and complexities of an IPsec solution.
Documentation:
Download the Barracuda Networks SSL VPN Datasheet (.PDF)




