Features:
Protection against OWASP & zero-day attacks
Protect against all OWASP top 10 attacks, zero-day attacks, data leakage, and DDoS attacks. The layered traffic processing engine and Smart Signatures use fewer attack-detection signatures to detect and block web attacks, including zero-day attacks. Each Smart Signature can detect attacks found in 40 attack-specific signatures, reducing detection time and improving overall detection. Application Learning adds automated Positive Security, with the ability to enforce this security from the URL down to the parameter level.
Advanced Bot Protection
Barracuda Advanced Bot Protection uses cloud-based machine learning to stop bad bots, easily blocking automated spam, web and price scraping, inventory hoarding, account takeover attacks, and much more
API Protection
Barracuda Web Application Firewall protects XML and JSON REST APIs against all application attacks, including OWASP Top 10 API threats. API Discovery capabilities make it easy to configure protection and limit the chances for misconfiguration.
Server Cloaking
Often the first step of a targeted attack is to probe public-facing applications to learn about the underlying servers, databases, and operating systems. Cloaking prevents attack reconnaissance by suppressing server banners, error messages, HTTP headers, return codes, debug information, or backend IP addresses from leaking to a potential attacker.
URL Encryption
Encrypt URLs before they are sent to clients, and ensure the original URLs or the directory structure are never exposed externally to prying eyes*. End users of the web applications interact and navigate the site using only encrypted URLs, which are decrypted by the WAF. The decryption process immediately identifies URL query or parameter tampering, malicious content injection or blind forceful browsing attacks. *Models 660 and above
Geo-IP and IP Reputation Checking
Using client source addresses, organizations can control access to web resources. The Barracuda Web Application Firewall can control access based on GeoIP to limit access only to specified regions. It is also integrated with the Barracuda Reputational Database and can identify suspicious IP addresses, bots, TOR networks and other anonymous proxies that are often used by attackers to hide their identity and location. Once an IP address is identified as a risk, administrators have the ability to block, limit, throttle, or issue a CAPTCHA challenge before allowing access.
Malware Protection and Anti-Virus
Seamless integration with Barracuda Advanced Threat Protection (BATP) to provide security against advanced threats. Simply add BATP to the Barracuda WAF to block advanced zero-hour threats. By analyzing files in a CPU-emulation based sandbox, it can detect, and block malware embedded deep inside files uploaded to websites or web applications.
Multi-Protocol Support
In addition to HTTP and HTTPS traffic processing, Barracuda Web Application Firewall can also inspect FTP and FTPS traffic and can be configured to allow/deny specific FTP commands. It also provides inspection capabilities for application protocols like XML and JSON and can be configured to proxy HTTP2 as well as HTML5 websockets traffic.
Application DDoS Protection
Protect against advanced application-layer DDoS (SlowLoris, RUDY and Slow Read) attacks which are different from volumetric DDoS attacks with heuristic fingerprinting and IP reputation to identify real users from botnet. Secure against application DDoS using a variety of risk assessment techniques such as application-centric thresholds, protocol checks, session integrity, active and passive client challenges, historical client reputation block lists, geo-location, and anomalous idle-time detection.
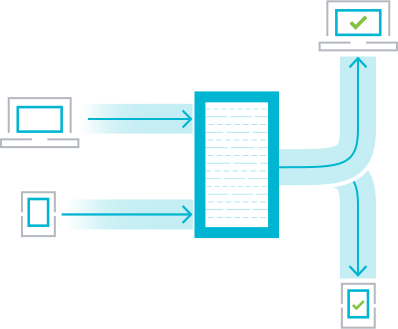
Volumetric DDoS Protection
Volumetric DDoS attacks are on the rise because the computational resources that are available to attackers make it very easy to launch full scale attacks that can bring an entire network down. Many times, the entry point for these attacks are web sites of organizations that bear the brunt of the load. Barracuda WAF offers a subscription-based DDoS protection cloud service that scrubs traffic before it reaches the intended websites. This allows the cloud service to identify patterns of DDOS attacks in the connections and block them.
JSON Security
Mobile application and REST APIs today rely on JSON (JavaScript Object Notation) to transfer data. However, this opens a whole new attack surface which is often overlooked and hard to secure by traditional scan-testing or pen-testing approaches. The Barracuda Web Application Firewall secures the entire attack surface of mobile applications and REST APIs, filters malicious inputs in requests with JSON payloads, helps ensure API SLAs to partners, and provides anti-pharming protection from rogue consumers. Interactive web applications using JSON with AJAX are similarly protected.
XML Firewall
Applications that rely on XML can now be secured with an XML Firewall capability that secures applications against schema and WSDL poisoning, highly-nested elements, recursive parsing, and other XML-based attacks. This secures communications between client and application or between applications from different systems closing an often-overlooked attack vector.
Active Threat Intelligence
Real-time attacks need real-time responses. Barracuda Active Threat Intelligence collects threat data from a large, worldwide network of sensors and customer traffic. This data is processed using Machine Learning in near real-time and pushed out to connected units immediately, allowing for rapid detection of new threats and attackers.
Client-Side Protection
Attackers exploit third-party scripts to perform client-side digital skimming attacks, such as Magecart, to steal PII and financial data directly from the browser. These attacks are difficult to detect because these scripts are loaded directly by the browser and attackers are using sophisticated techniques to avoid detection with scanners and similar defensive methods. Barracuda Web Application Firewall offers Client-Side Protection, a feature that automates the CSP and SRI configuration, reducing admin overheads and configuration errors. In addition to these capabilities, the Barracuda Active Threat Intelligence layer provides visualization and reporting for these configurations, providing admins with deeper visibility into the usage of these scripts.